The New Reality of Mobile Fraud
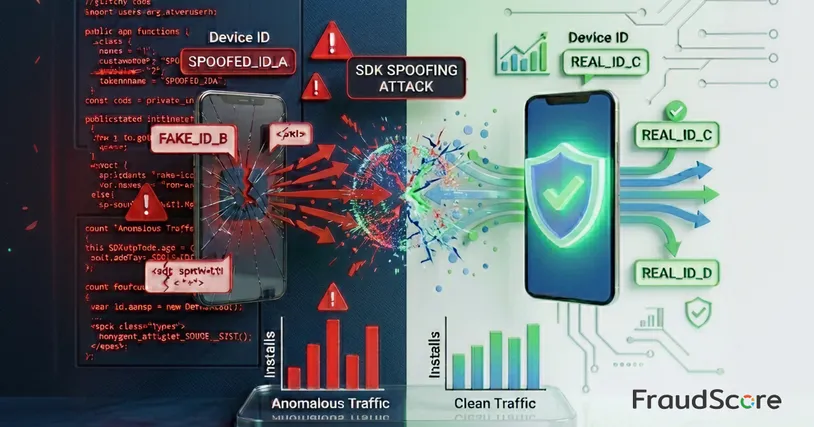
The mobile market is no stranger to fraud. Bots, click farms, and incentivized traffic – these schemes are well understood and detectable in most cases. But in recent years, a more sophisticated and dangerous form of fraud has taken center stage: SDK spoofing.
This type of fraud is stealthy, scalable, and often masquerades as high-quality traffic. That’s why SDK spoofing is now seen as one of the biggest threats to mobile app advertisers.
Why You Can’t Ignore SDK Spoofing
SDK spoofing isn’t new, but it’s exploding in popularity right now. The reason is straightforward: traditional anti-fraud methods have stopped working. Fraudsters have moved beyond basic bots and device farms to emulating user signals at a deeper level. This traffic is tough to filter by IP, geography, or device parameters – it doesn’t break any formal rules and sails through basic checks.
A typical scenario looks deceptively positive: advertisers see spikes in installs, registrations, and even in-app events. But there’s no real users behind those numbers.
In SDK spoofing, bad actors don’t actually launch the app or interact with it. They feed fake signals into tracking systems that mimic real user actions, using valid device IDs and other parameters typical of live devices. Visually, these events are indistinguishable from legitimate ones.
The result? Businesses base decisions on data that doesn’t reflect true audience behavior, leading to distorted insights.
The Scale of the Problem
According to FraudScore data, 47.77% of global mobile traffic in 2025 was fraudulent. That means nearly half of installs, clicks, and events had nothing to do with real users.
Advanced fraud forms like SDK spoofing are especially alarming. In some campaigns, it can account for over 80% of total traffic. These schemes cause direct financial losses, skew analytics, and make it impossible to accurately measure marketing performance.
For markets with mature mobile advertising, this translates to systemic losses: budgets get burned on simulated activity that delivers zero user retention or revenue growth.
How Protection Approaches Are Evolving
You can’t detect SDK spoofing with a single signal or parameter. Effective defense demands comprehensive analysis. FraudScore uses over 150 algorithms and metrics to scrutinize behavioral and technical anomalies, event sequences, and deviations from natural user patterns. This approach uncovers fake activity even when it looks identical to genuine installs.
Anton Sanin, Head of Customer Success at FraudScore:
Reality is, whether a client uses an anti-fraud service or works directly with an agency, anyone buying mobile installs faces the same SDK spoofing risk. Our goal is to drastically reduce this threat across the market.
What advertisers should focus on right now
Experts urge ditching single-metric evaluations of mobile ad performance and looking at the big picture:
- Analyze retention and cohort behavior, not just install volume (FraudScore’s cohort reports help spot these anomalies and test hypotheses).
- Cross-reference analytics data with CRM and financial metrics.
- Evaluate event sequences and user engagement.
- Deploy specialized anti-fraud tools for ongoing traffic quality monitoring.
What’s next
SDK spoofing isn’t a passing trend – it’s the new reality of mobile marketing. As fraud schemes grow more complex, advertisers and agencies will need to invest in deeper analytics and rethink traffic evaluation.
Anti-fraud is shifting from a nice-to-have to a core component of mobile ad performance control. Those who build these systems now will gain not just protection from losses, but a clearer, more sustainable growth model.
FraudScore has rolled out SDK spoofing detection algorithms based on real-world cases. Current results show up to 90% accuracy in identifying fake signals, with minimal impact on legitimate traffic.
Ready to take control of traffic quality? Request a demo, and see how FraudScore identifies advanced fraud like SDK spoofing.