FraudScore Approach
Fraud is a type of “crime” in any possible scenario. A marketer starts to dig his own pit when fraud is not detected. He invests more money on fraudulent channels that show great statistics, gets unreliable sky-rocketing results, and invests more funds on these channels. It’s a vicious circle of advertising, and it needs to be broken.
Fighting fraud requires understanding and recognizing various types of fraud. This article gives a quick overview of the types of fraud most common in the industry.
1. Click Spam
Definition and how it works
The fraudster tries to execute clicks for users who are completely unaware. The user might be organic to the app or an ad, but the fraudster uses different means to catch the last action and get all the credit. The main method is to infect a real user’s device and get the click that provides real organic conversions.
How might the “infection” get to a real user’s device? Imagine the user opens a mobile web page or an app:
- Imitate the engagement – a fraudster can imitate user engagement by sending impressions-as-clicks, making it look like the user viewed an ad and executed a click.
- An old trick – a simple real redirect of the user to the app-store page even if he hasn’t clicked on the ad. This uses promotional tracking links and negatively affects the user experience.
- Infected apps – launchers, battery savers, screencasting apps, memory cleaners. These apps generate clicks in the background without user awareness.
- Invisible threat or pixel stuffing – advertising links placed in pixels on mobile web pages, processed without showing any signs to users. Common in video content pages.
Standard symptoms
Low Conversion Rates or a long-tail for TTI graphs. Real users usually open the app within the first 30 minutes to 1 hour post-install. Exceptions exist, which is why using FraudScore is recommended.
The problem that it causes
Click spam uses real users to get credit. Advertisers investing in a source may see impressive metrics and spend more, but eventually the budget is wasted or misallocated, resulting in losses.
2. Fake installs
Definition and how it works
A fake install is a completely fraudulent install by a fabricated user. This type of fraud spreads damage to all parties – advertiser, network, developer, and publisher.
Fraudsters use data centers and software to simulate real devices, creating “new” devices with unique IDs and OS versions. These devices simulate user behavior: click the ad, download the app, and start the app post-install.
Standard symptoms
Check traffic pricing with other providers. Lower-than-market prices may indicate fake traffic. Also examine:
- Post-install activity – if a majority of users follow identical patterns (starting the app on day 5, 10, or 17), they are likely fake.
The problem that it causes
Advertisers pay for installs that are fake, resulting in wasted budgets. Networks lose reliability if installs are not genuine. Some fraudsters even emulate post-install activity to make traffic appear real.
3. Click Injection
Definition and how it usually works
Only Android devices are prone to click injection, a complex type of click spam. Fraudsters require malware on a mobile app or their own app to access a user’s device. After installation, the malware reads “install broadcasts” and assigns subsequent installs to the fraudster. It checks which apps have paid campaigns and manipulates attribution.
Standard symptoms
Abnormalities in very low TTI and very high CR. Google has improved install data since 2017, but click injection schemes continue to evolve.
The problem that it causes
Advertiser budgets are wasted on injected clicks. Developers may invest more in regions that appear effective, but results are fraudulent. Networks are also affected as traffic quality declines.
4. SDK Spoofing
Definition and how it usually works
SDK spoofing imitates installs without real user activity but uses real devices. Fraudsters gain access via apps (battery savers, memory cleaners, etc.), collect device data, break SSL encryption between SDK and servers, and simulate installs repeatedly.
Standard symptoms
Fraudsters break SSL encryption; once SDK is updated, fraudulent activity stops. SDK spoofing is complex because it leverages real device data. Always check that installed SDK versions match the latest release.
The problem that it causes
No real installs, clicks, or user engagement occur, yet budgets are spent. Networks may show good metrics initially, but traffic is unreliable.
5. Device farms
Definition and how it usually works
Real devices and people are used, but the purpose is to earn money for installs/clicks without retention or purchases. Workers operate dozens of devices, repeating instructed actions.
Standard symptoms
Low retention rates or unusual time-to-start may indicate a device farm. Check IPs for reliability; VPNs or proxies may be used. Advanced fraud detection platforms can identify suspicious IP activity.
The problem that it causes
Real devices and users generate traffic, but no meaningful engagement occurs. Advertisers and networks are deceived and budgets are wasted.
To conclude
This article provides a short overview of common fraud types. Fraud is diverse and evolves constantly. Data from August–November 2018 shows a variety of fraud types, summarized in the diagram below:
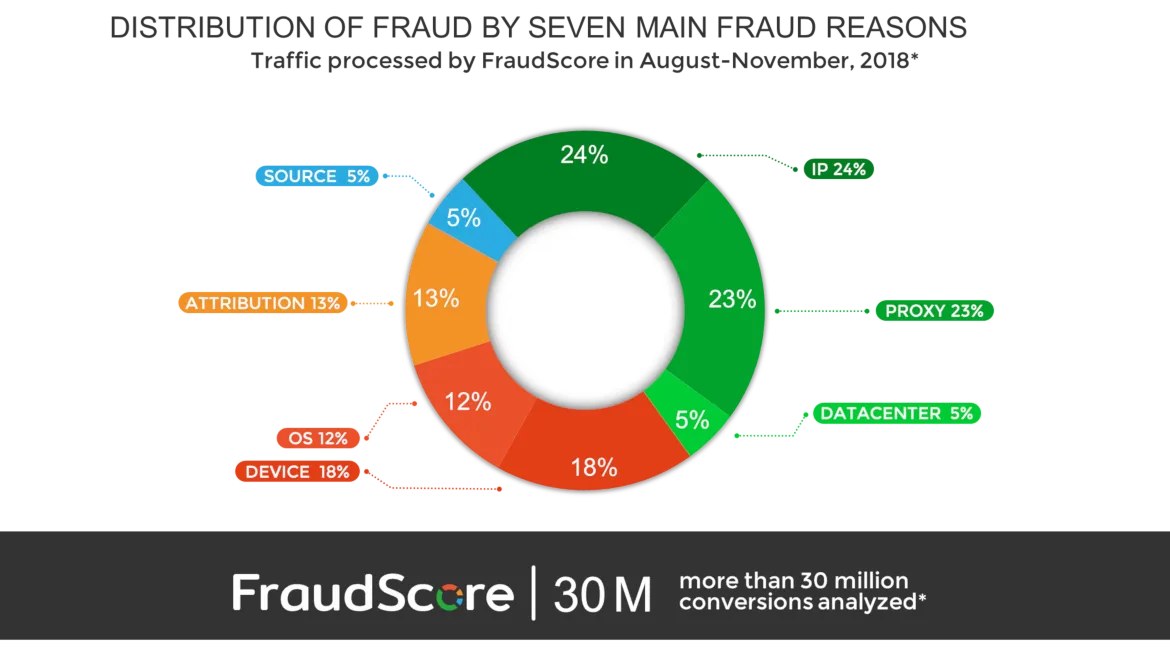
Each category has specific symptoms that FraudScore analyzes to detect fraudulent activity. Our approach combines metrics and patterns for systematic fraud detection.
For more details, follow this link to see our full methodology.
FraudScore fully takes responsibility for detecting and fighting fraud affecting our clients. We provide ongoing support, expertise, and education.
Ad fraud is now recognized as a serious industry problem. Networks lose trust, marketers overspend, and budgets are misallocated if fraud is undetected.